Cintoo provides the highest level of data security for your projects with SOC 2 Type 2 conformity

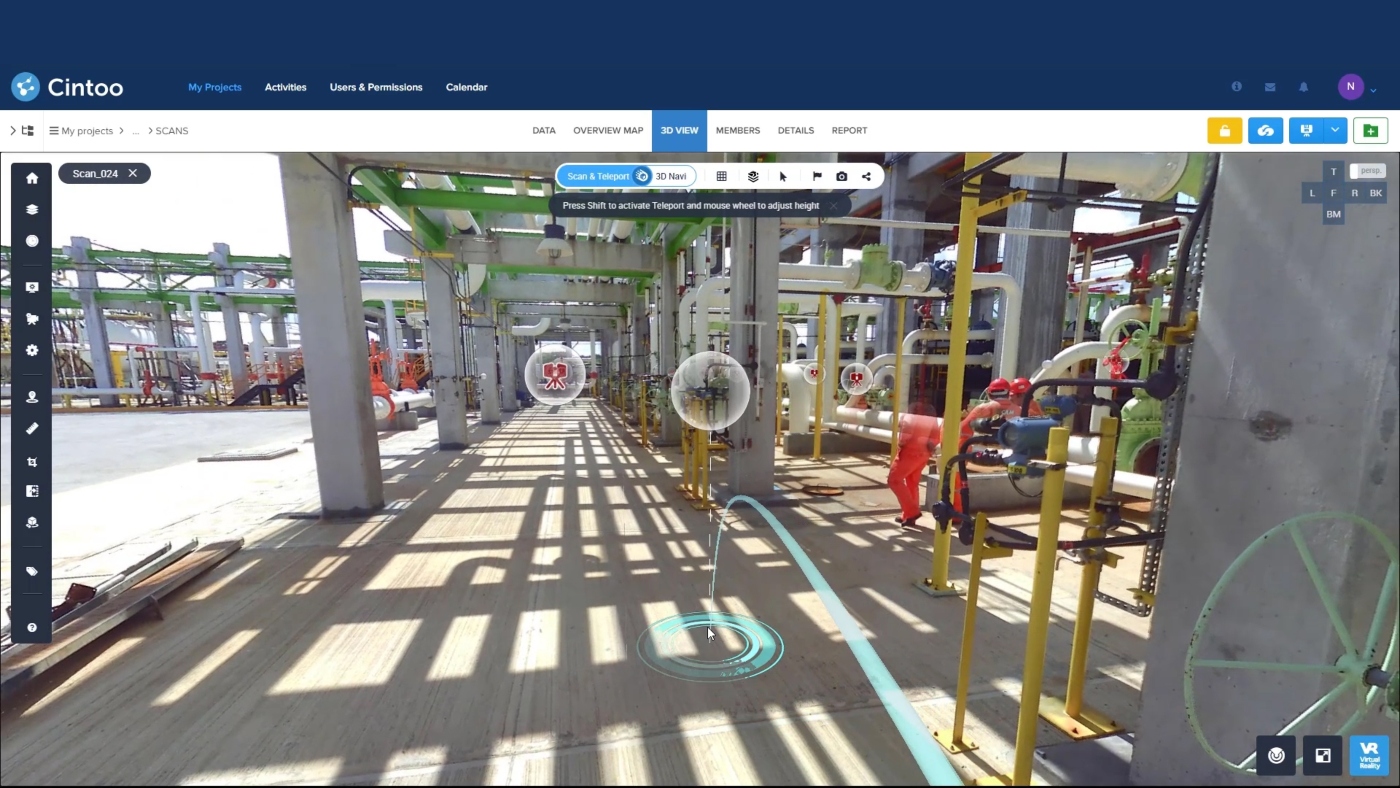
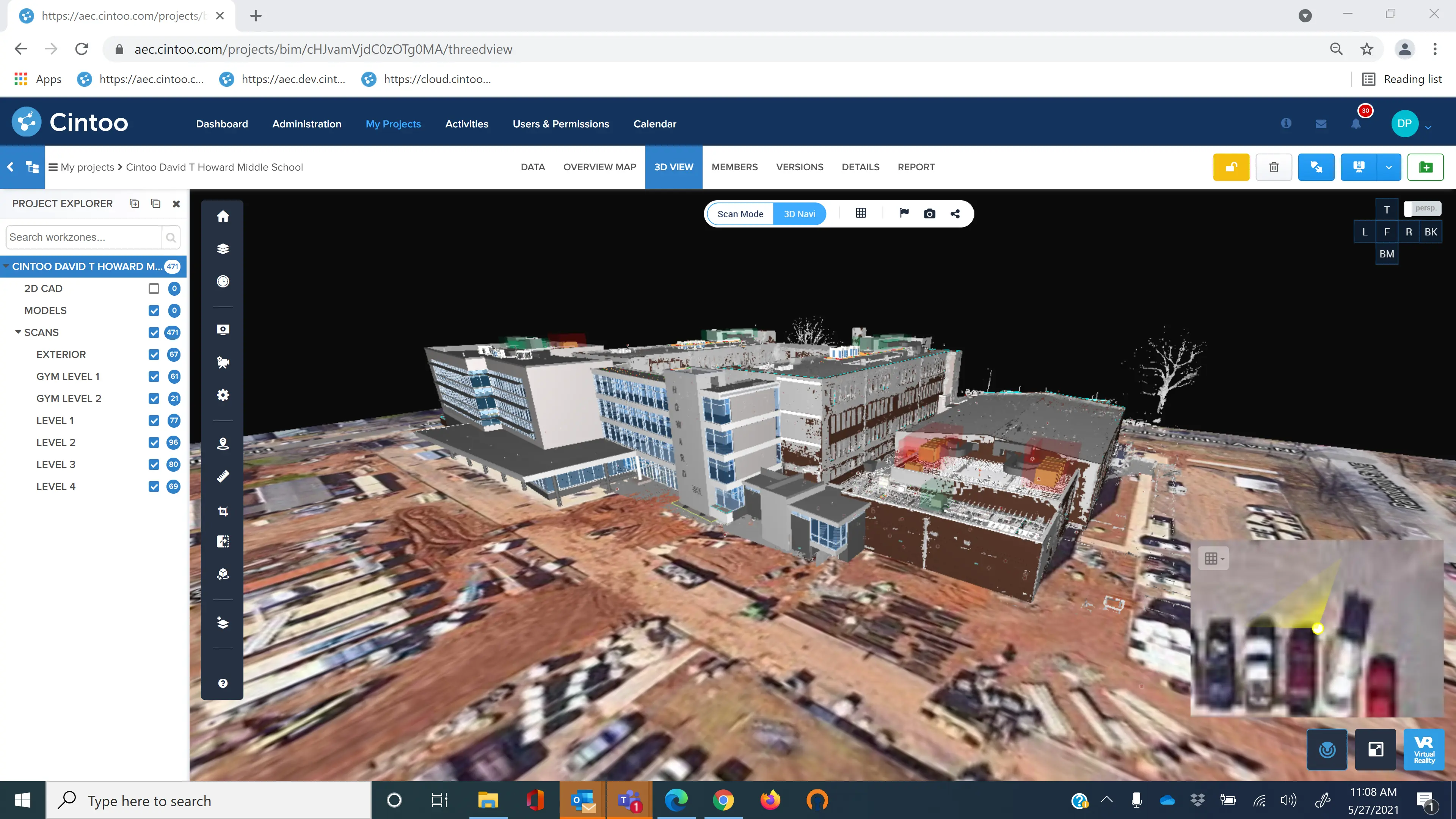
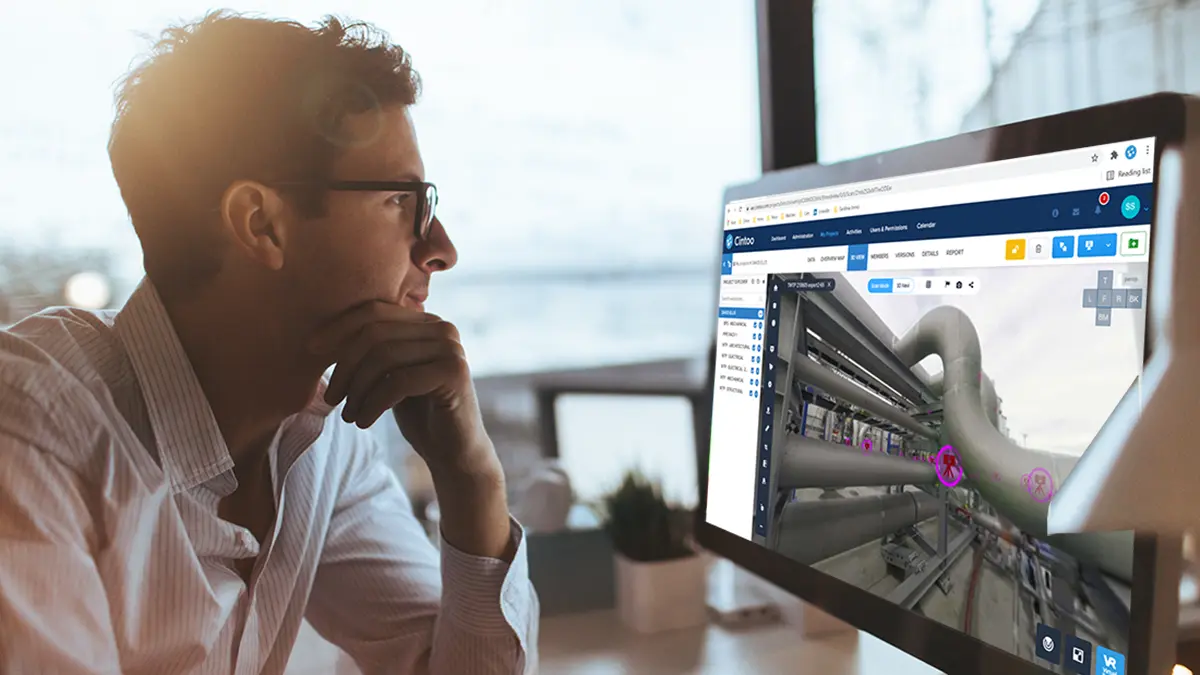
Oil and gas companies, manufacturing companies, renewable and nuclear energy operators, banks, datacenters, general contractors, and government facilities all have one thing in common when it comes to their laser scan projects: they need their data to be stored in as secure an environment as possible.
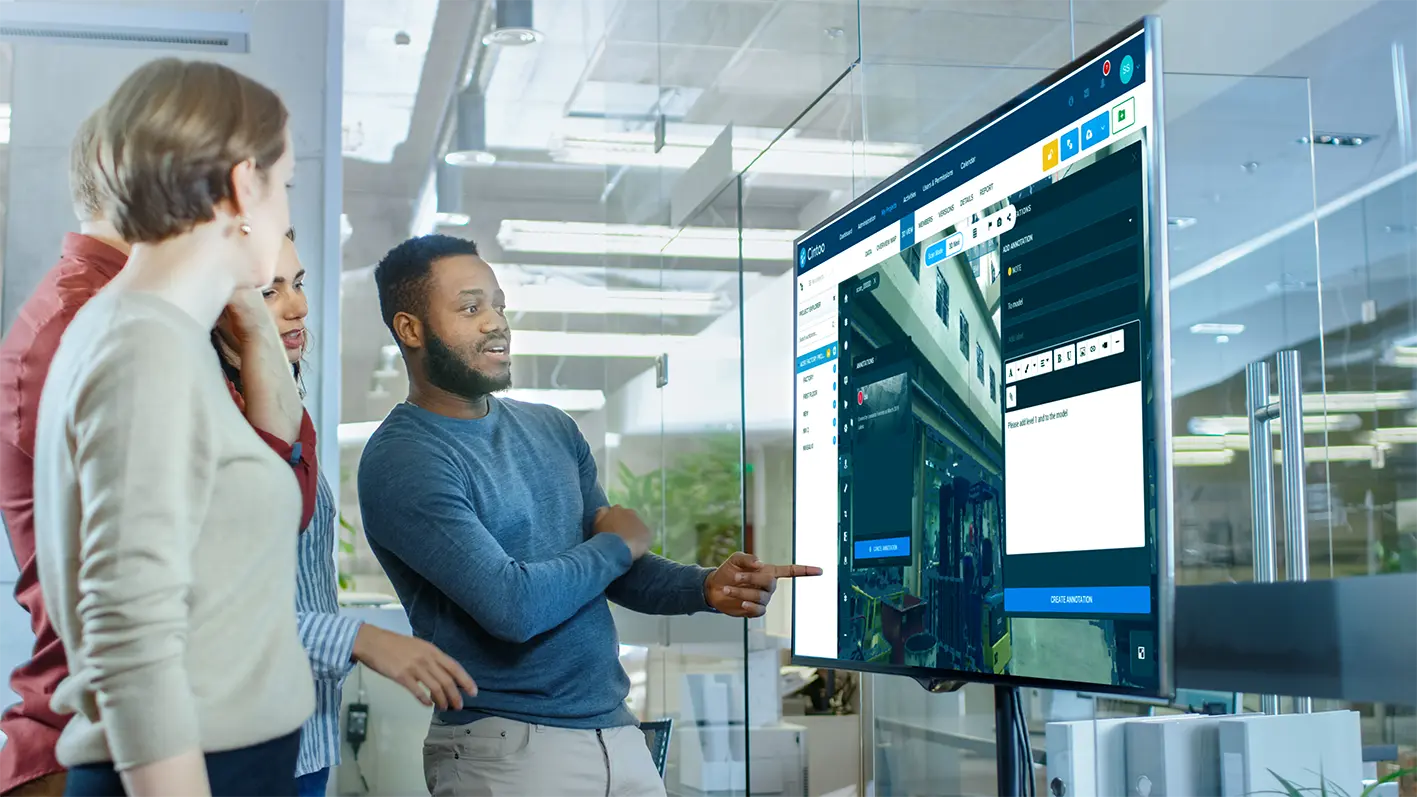
At the same time as needing the most advanced security to protect highly sensitive assets, they need to provide those working on the project with seamless access to their project data, along with the ability to collaborate with team members both on-site as well as remotely.
SOC 2 is an auditing procedure, developed by the American Institute of Certified Public Accountants (AICPA), that ensures your cloud service providers are securely managing your data. The trust services criteria for reporting are security, availability, processing integrity, confidentiality, and privacy. (You can find more information about SOC 2 on AICPA’s website: https://www.aicpa.org/)
As of July 28th, 2021, Cintoo is now SOC 2 Type 2 compliant, demonstrating that our platform has the same level of security compliance as Microsoft Azure and Amazon Web Services. This encompasses the way we develop the software, segment the information, and control the publishing process.
The SOC2 Type 2 compliance review into Cintoo Cloud was conducted by an external US-based auditor that reviewed and examined Cintoo’s control objectives and activities and tested those controls to ensure that they are operating effectively. SOC 2 is based on Policies, Communications, Procedures and Monitoring. The Type 2 report is issued to organizations that have audited controls in place and the effectiveness of the controls have been audited over a specified period of months.
As part of this SOC 2 compliancy, Cintoo also only uses suppliers who are both SOC 2 Type 2 and GDPR compliant, such as Microsoft Azure and AWS.
In addition to this, penetration tests provide further peace of mind to our customers that their data is cyber secure. An independent cybersecurity company attempts to hack our system every six months and at the end of these tests, we are provided with a report to confirm that despite trying by all means to hack our system they were unable to do so.
Both the SOC 2 Type 2 and Pen Test reports can be provided to our customers’ IT teams upon signing an NDA.
Contact our team to start benefitting from leveraging your laser scan data using Cintoo Cloud, knowing that your data will be safe and secure: www.cintoo.com / sales@cintoo.com